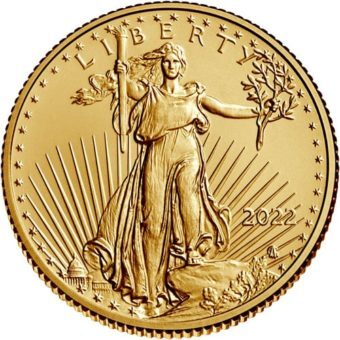
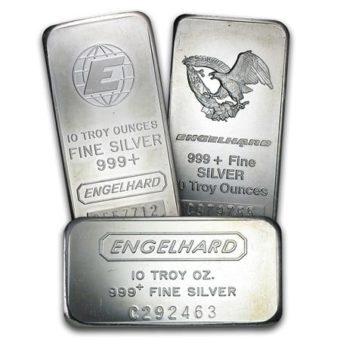
BEST SELLERS
NEW ARRIVALS
WHY GSI EXCHANGE
TRUST
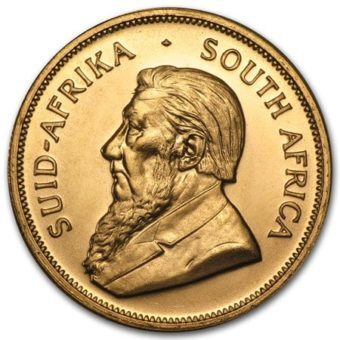
GSI Exchange is a BCA AAA rated, leading national coin and precious metals company who continues to be highly praised for our Lowest Price Guarantee on the direct sales of Gold and Silver coins, as well as our signature wholesale precious metals trading whether for a standard portfolio, or as part of a Gold IRA, a Silver IRA or a combined Gold & Silver IRA account.
DIVERSITY
GSI Exchange is more than a trusted name in wholesale pricing and trading in Gold & Silver coins, bars & bullion.
We are also a leading authority on precious metals IRAs! That's right! At GSI Exchange, we offer our clientele a full range of customized precious metals portfolios, as well as physical possession Gold IRA and Silver IRA accounts.
EXPERIENCE
The GSI Exchange management team has experience successfully placing more than $1 billion in commodities and precious metals transactions around the world.
The relationships we have forged enable us to reliably offer an almost unlimited inventory of the highest-quality silver, gold, palladium and platinum coins at the most competitive prices.
TESTIMONIALS

Walter B.
"Thank you for making me feel secure about my family's future!"
Eric G.
"Very knowledgeable and pleasant to work with."

David S.
"Working with GSI Exchange was the best choice I made!"